Cybersecurity is a top of mind concern for every IT organization. Recent events show how cyber threats are not only persistent but constantly evolve. IT teams are challenged to react to these threats and be proactive in minimizing their security risks and vulnerabilities. Doing this effectively at scale requires security to be built in and automated as much as possible. New cybersecurity intelligence now included with CloudIQ to detect, report, and remediate infrastructure security vulnerabilities provide new levels of visibility into potential threats. Leveraging CloudIQ with Cybersecurity helps IT teams better protect their users, organizations, and customers. Here’s how.
What is CloudIQ and what’s new?
CloudIQ is a cloud-based tool used to manage almost every Dell infrastructure technology. It provides users with a dashboard that proactively monitors and predictively analyzes your Dell infrastructure’s health, performance, and capacity, and now security settings. Simply put, it’s a smart, easy to set up and use, and simplifies management of your Dell infrastructure. Users really love it. Currently CloudIQ is connected to almost 100,000 installed devices. To put that into context, if you assume the average capacity per system to be at least 200TB, that means CloudIQ is helping manage over 20 exabytes of information (or >21,474,836,480 GB if you’re a storage engineer 😊).
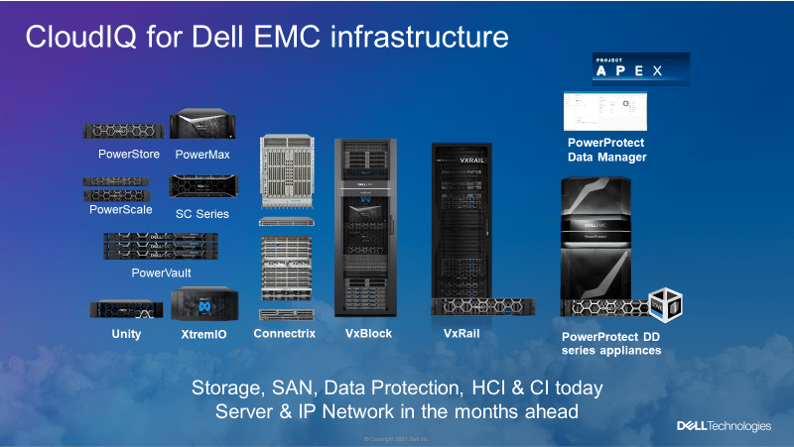
Dell is now extending CloudIQ’s capabilities by building in automated cybersecurity intelligence to help organizations secure their infrastructure. It delivers a truly innovative and unique capability unmatched by other security monitoring offerings. The development and delivery of these powerful new security capabilities involved teams across the entire Dell Infrastructure Solutions Group (ISG) organization. The result is a common security dashboard that is architected to be leveraged across the entire Dell infrastructure portfolio. This includes storage, compute, networking, backup, and archive platforms as well as APEX Data Storage Services.
Let’s look at what it does, how it works, and how users can access it.
What does CloudIQ Cybersecurity do?
The use case is a common scenario when organizations are installing and managing data center infrastructure. The potential for misconfigurations can inadvertently open organizations to potential threats and vulnerabilities that can be exploited by cyber criminals. Infrastructure misconfigurations are considered to be a leading threat to data security (e.g., within the top 10 security risks according to the Open Web Application Security Project foundation).
Here’s a real world example. A new storage array is delivered (Yay!!). The array is set up and added into the environment. As part of that set up, multiple configuration options are set. Things like changing the default password, enabling LDAP authentication for admins, separating privileges by turning on RBAC, enabling encryption, etc… Depending on the array, there could be dozens of config options that depending on how they are set up can impact the security and hardening of the array. Each of these config settings is performed on an array by array basis.
Having visibility into how the array has been set up is now provided by CloudIQ via the Cybersecurity System Risk dashboard. This allows infrastructure and security admins to easily assess the arrays potential security vulnerability and take the necessary actions to remediate the settings. It also allows admins to be notified if something is either changed or falls out of compliance with their security standards.

In a nutshell, here’s how CloudIQ with cybersecurity helps users.
- It reduces security risks by alerting you about potential vulnerabilities via an easy-to-read cybersecurity dashboard that pinpoint risk and recommend actions for fast resolution and assure your ongoing cybersecurity awareness.
- It allows you to set security policies using an easy-to-use tool for customizing infrastructure security policy (i.e., choosing configurations that you want deployed on your infrastructure).
- It makes your life easier proving you with an application that continuously monitors cybersecurity for you versus spending hours inspecting every system yourself – and it conveniently does this in the same application you know and love for doing daily infrastructure health, performance, and capacity monitoring.
How does CloudIQ Cybersecurity work?
CloudIQ works in a couple of different ways. Users can enable the feature and use the default security policies to monitor and report on the infrastructure device. The default settings are based on NIST 800-53 r5 and NIST 800 – 209 security standards as well as Dell’s best practices for each specific infrastructure product. Using the default settings provide an easy to enable and comprehensive starting point.
Users can also easily create customized policies that are specific to their own internal security and governance policies. The Evaluation Plan Editor allows admins to enable some or all available evaluation (i.e., cybersecurity configuration) tests. Creating a custom security policy is a simple three-step process using the Cybersecurity Evaluation Plan Editor tool; select policy in CloudIQ Cybersecurity tab, select system and edit the policy, select enable, and CloudIQ will start collecting and assessing the security telemetry. The process is transparent, secure, and automated. Here’s the step by step.
- Step 1: Data Collection – Security data from end users’ systems is sent through the secure Dell Technologies Secure Remote Services network to CloudIQ, hosted in Dell Technologies secure data center.
- Step 2: Data Processing – After data is collected, it will be organized, normalized, and securely stored by CloudIQ with end-user data privacy controls in the Dell Technologies data center.
- Step 3: Evaluate Data – End-user system’s actual security configuration data is compared to the configurations which end-users specified with the Cybersecurity Evaluation Plan Editor.
- Step 4: Data Analysis – Misconfigurations’ impact on numeric risk levels are calculated and recommended actions are derived.
- Step 5: Display and User Interaction – Results of the analysis are displayed in the CloudIQ user interface and emails are sent to users who have opted in for notifications.
Once the security policies have been enabled the telemetry has been collected, security risks are then calculated according to the number of deviations discovered and weight of every single of the deviations. A minimum of five configuration evaluation tests must be selected in the Evaluation Plan Editor to enable risk level calculation.
How do I get CloudIQ Cybersecurity?
Cybersecurity is a new standard feature for CloudIQ and is available to existing users at no extra cost. Currently CloudIQ with cybersecurity is supported on PowerMax and PowerStore. Other platforms are being qualified and added over time.
If you’re an existing CloudIQ user and running the current array management version (PowerMax with Unisphere 9.2.1.0 and/or PowerStore OS 2.0.0.0) you have access to the new security dashboard. All an admin needs do is opt in to have the dashboard added and visible within CloudIQ. Once the cybersecurity dashboard has been enabled CloudIQ also proactively sends security notifications via email. The notifications include helpful details and recommendations is an issue is detected to help with faster problem resolution.
Here’s the KB with the step by step process to opt in and enable the feature.
In summary, CloudIQ with built in cybersecurity helps address a growing challenge for organization to protect the security of their infrastructure and minimize potential risks and vulnerabilities. Adding these capabilities to CloudIQ provides a single dashboard that can be leveraged across a wide range of Dell’s infrastructure technologies. Helping organizations improve their cybersecurity while making it easy to enable and simple to use provides one more reason (or 0001 if you’re a storage engineer) for why users continue to love CloudIQ.
More information on CloudIQ including technical information, demonstration videos, third-party reviews, and case studies can be found here.


[…] Introducing Cybersecurity for CloudIQ – mybitstream […]
LikeLike