Cyber security is a top of mind concern for every IT organization. Research shows that a cyber or ransomware attack occurs every 11 seconds. This elevated frequency of attacks becomes an even greater issue as hackers evolve their techniques to find new ways to infiltrate IT infrastructures. Potential threats and breaches are no longer from external entities only. New potential threats can come from within where attackers already have gained back door access to the infrastructure. Building a secure, zero trust infrastructure helps address these external and internal treats and protect an organization’s infrastructure and more importantly, the information assets within it.
What is Zero Trust Infrastructure?
Zero-trust Infrastructure is built around a set of principles that presumes the compute, network, and storage components are always vulnerable to compromise and sets out to safeguard access to critical data and resources. Dell’s Zero Trust Infrastructure strategy is helping many IT organizations develop security strategies not based on “if”, but “when” an attack occurs. It’s based on the following 5 tenants:
- Assume every user and/or device is a potential threat.
- Apply the principle of “least privilege” to restrict users (and their devices).
- Apply multifactor authentication models and authorization rights that are time based, scope based, and role based.
- Authenticate and authorize at communication intersections of the infrastructure.
- No entity is inherently trusted, and verification is required to access all assets.
One of the core notions behind building a Zero Trust Infrastructure is the concept of a trusted computing hardware and software stack. As attacks grow more sophisticated, hackers are targeting technology components to try and gain unnoticed back door access. The attempt is to to compromise data security or exploit vulnerabilities to introduce malware or ransomware. Recent high profile examples show that both hardware and software components can be vulnerable and attritive targets for hackers. A trusted computing environment based on Zero Trust can address these vulnerabilities. It gives technology providers control over what hardware and software does and does not run on a system by refusing to run modified hardware components of unsigned versions of software.
With Zero Trust, technology components will consistently behave in expected ways. Those behaviors will be enforced by an securely coupled computer hardware and software stack. Enforcing this behavior is achieved by using the hardware with a unique encryption key that is inaccessible to the rest of the system and requires software loads and changes to authenticate at each step in a particular process. The technology based on a “Hardware Root of Trust”” and has existed in the server space for several years. Dell PowerEdge introduced this in 2017 with 14G and is now being introduced to the storage array layer for the first time.
What is PowerMax Hardware Root of Trust and Why is it Important?
PowerMax includes a range of security capabilities that have developed and hardened to provide the world’s most secure storage array. The new PowerMax 2500 and 8500 is based on new Intel CPU chips sets that provide Hardware Root of Trust. It provides an immutable, silicon-based Root of Trust to cryptographically attest to the integrity of the BIOS and firmware. This Root of Trust is based on one-time programmable, read-only key that provides protection against malware tampering. It starts a chain of trust needed to ensure the array boots with legitimate code. If the first piece of code executed has been verified as legitimate, those credentials are trusted by the execution of each subsequent piece of code.
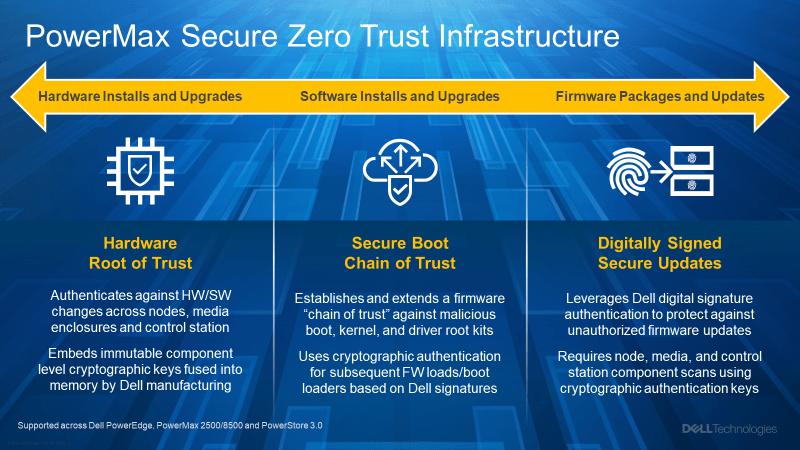
The PowerMax hardware provides the following security features for firmware images and the operating system through the Secure Boot and x86 Secure Boot technologies that are provided through the enclosure management software on the system
- Authentication and root of trust provides the capability to authenticate boot loader and firmware, and immutable hardware root of trust.
- Ensure a verified and measured boot.
- Authenticate firmware images and operating system boot loader at boot time.
- Digitally signed firmware upgrades ensure that root of trust authenticates all signed upgrade firmware images.
How Does Root of Trust Work Process Work?
Secure Boot represents an industry-wide standard for security in the pre-boot environment. Computer system vendors, expansion card vendors, and operating system providers collaborate on the specification to promote interoperability. Secure Boot is the process of verification that the image to be booted is exactly the image that is expected. It is used during Hardware Root of Trust, firmware load, and firmware upgrade. Secure Boot also extends through all the various images that need to be booted all the way, through the execution of the operating system image, such as bootloaders, to firmware to Initial BIOS to UEFI.
PowerMaxOS for PowerMax 2500/8500 supports industry standard UEFI Secure Boot, which checks the cryptographic signatures of UEFI drivers, kernels and other code loaded prior to the operating system running. UEFI (or Unified Extensible Firmware Interface) is a firmware interface that works as an interpreter between the operating system and the computer firmware. UEFI Secure Boot prevents unsigned (untrusted) UEFI device drivers or operating system kernels from being loaded, displays error messages, and does not allow the device to function.
Measured Boot is the process of storing hash values used for authentication during a Secure Boot sequence. Values are stored in the boot log within a Trusted Computing Group (TCG)-defined trusted platform module (TPM), public keys, and the various signatures. The TPM values can be used through a token process by an upstream operating system or applications to validate the expected execution of a Secure Boot process. PowerMaxOS for PowerMax 2500/8500 supports two versions of TPM, TPM 2.0 FIPS + Common Criteria + TCG certified and TPM 2.0 China certified. The TPM can be used to perform public key cryptographic functions and compute hash functions, and can generate, manage, and securely store keys.
PowerMax also implements digital signatures on firmware updates for all components and subcomponents to assure that only authentic firmware is running on the platform. Secure firmware upgrades use cryptographic authentication of digital signatures applied to the firmware bootloader and images of the running firmware before running any update process.
Enhanced firmware authentication is embedded within many third-party devices that provide signature validation using their own Root of Trust mechanisms. This prevents the possible use of a compromised third-party update tool from being used to load malicious firmware into, for example, a NIC or storage drive (and bypassing the use of signed Dell update packages). Many of the third-party PCIe and storage devices shipped with PowerMax use a hardware Root of Trust to validate their respective firmware updates. This includes component related to PowerMax nodes, media, and control station that are scanned and authenticated using the embedded cryptographic keys. If any firmware in any device is suspected of malicious tampering, changes and upgrades to the platform firmware images are rolled back to an earlier trusted version stored in PowerMax.
Zero Trust: The New Standard in Cybersecurity
In the wake of a rash of bold cyberattacks and ever-evolving risks that have targeted everything from the national energy grid to the food supply chain, organizations are going back to the fundamentals of information security. Unlike trust-then-verify frameworks, the Zero Trust approach performs verification before it trusts a user, or device, and grants access.
The Dell Technologies zero-trust approach has been developed to align with the U.S. Department of Defense (DoD) standards and, in the near future, government agencies, their vendors and those in heavily regulated industries — like infrastructure, transportation, energy, healthcare and banking. As a result, businesses can expect more scrutiny to be placed on them to comply with zero-trust security specifications.
PowerMax storage arrays continue the security innovation and legacy of Symmetrix, DMX, and VMAX arrays that have come before it. It reduces security vulnerabilities risk while delivering mission-critical storage infrastructure with scale, performance, availability, and trust that IT organizations have relied on for over the last three decades.


[…] good friend Scott Delandy wrote a great brief around Dell’s Zero Trust implementation around PowerMax and this principle applies to the work Dell has done in PowerStore. I love Scott’s focus on […]
LikeLike